skip to main |
skip to sidebar
I am providing this blog to help people obtain information about computers and related topics.
Your comments and questions are most welcome. If I don't know the answer I will try my best to get it. Also, please give me your suggestions for future topics.
For older posts please check the panel on the right side of the page.
To view older posts page down to Blog Archive. Click on the blue arrow heads for the desired year/month .
Feel free to send me email: don@donnitkin.com
Pages
About This Blog
I am providing this blog to help people obtain information about computers and related topics.
Your comments and questions are most welcome. If I don't know the answer I will try my best to get it. Also, please give me your suggestions for future topics.
For older posts please check the panel on the right side of the page.
To view older posts page down to Blog Archive. Click on the blue arrow heads for the desired year/month .
Feel free to send me email: don@donnitkin.com
How to get to linked pages
CLICK THE UNDERLINED WORDS TO LEARN MORE
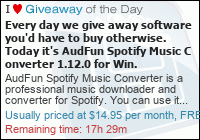
When something is underlined in my blog, click it. It's a link to the featured web site, explanation or definition page. You can get to the entire story by clicking either on the title of the blog or on the graphic below. When you click on the title it turns yellow. That is how you know it is a clickable link. When you click on the graphic a thin yellow bar appears underneath. This also tells you that the graphic is clickable.
When something is underlined in my blog, click it. It's a link to the featured web site, explanation or definition page. You can get to the entire story by clicking either on the title of the blog or on the graphic below. When you click on the title it turns yellow. That is how you know it is a clickable link. When you click on the graphic a thin yellow bar appears underneath. This also tells you that the graphic is clickable.
Free Computer Tutorials
Search This Blog
My Favorite Links
Subscibe to Don's Blog
Translate Blog
Guest Book
Powered by Blogger.
Loading